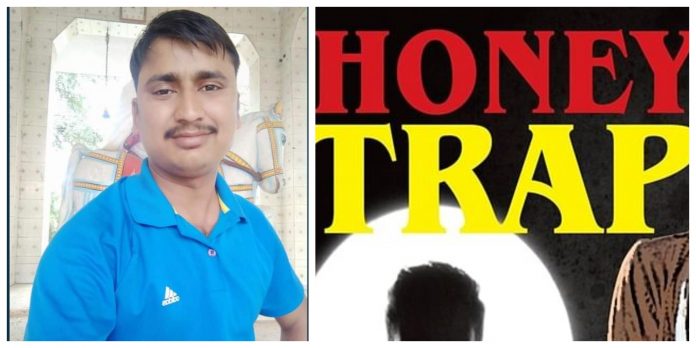
In a joint operation conducted by the Military Intelligence (MI) Lucknow and the Special Task Force (STF) of Haryana, an employee of the Military Engineering Services was arrested in Rewari, Haryana on espionage charges. The employee Mahesh Kumar was reportedly honey-trapped on Facebook and was sharing classified information to the Pakistan Military Intelligence.
A civilian #defence employee was arrested for passing on classified information to a #Pakistani Military Intelligence (MI) unit after he had been honey-trapped on #Facebook.
— IANS Tweets (@ians_india) September 17, 2020
Photos: IANS pic.twitter.com/3xkRAE45BA
According to reports, a joint interrogation of the accused is underway and his mobile phone is also being examined. The accused was in contact with the operatives of the Pakistani Military Intelligence for two and a half years. He had also received money on many occasions.
In June this year, Lucknow Military Intelligence had received an input that user of a mobile number used by Mahesh Kumar was sharing sensitive military information to a young woman associated with Pakistani MI. It was learnt that he addressed the Pakistani operative as “Madamji”, and he was sharing informed in exchange of money.
Based on this input, the MI had launched an operation code-named “Ops Madamji”, where it was found that Mahesh Kumar, who is a cleaning staff at MES Jaipur, is friends with at least three known and established Pakistani Intelligence Operative (PIO)-run Facebook accounts. When the MI further probed the matter, they found that Mahesh had received at least two payments of Rs 5000 each from his Pakistani handlers via Kerala.
As Mahesh Kumar was staying in Rewari in Haryana, the MI informed about the same to STF Haryana, and a joint team of both the agencies was formed to nab him. They had planned to nab him for interrogation on 13th and 14th September, but he was not in Rewari during those days. When Mahesh Kumar reached Rewari on Wednesday, he was apprehended by STF Haryana. His mobile phone was also taken, and he was jointly questioned by MI Lucknow, STF Haryana and MI Jaipur.
During questioning, MES employee Mahesh Kumar admitted that he was in contact with known PIO-run Facebook account with the name ‘Harleen Gill’ in July 2018. He said that he had sent the friend request to the PIO run account. They became friends on Facebook and used to communicate through text and audio or video chat on Facebook messenger. The account was run by a young woman who claimed that she was working with Principal Controller of Defence Accounts (PCDA) office in Jalandhar. The Facebook account of ‘Harleen Gill’ was later deactivated.
Next year in 2019 Mahesh Kumar received a fried request from another Facebook account with the name ‘Harman Kour’. They started communicating through Facebook messenger and later through WhatsApp. He was in contact with at least two PIO operatives on WhatsApp, and they used to exchange text and audio messages, apart from talking via video chats.
During the questioning, Mahesh Kumar has accepted that he shared details about Jaipur based Army Brigade, details of senior army officers, location of PCDA Jaipur, details of MES complaint records, Covid19 state of the Jaipur cantonment and posting order of civilian MES employees with his Pakistani handlers. He said that he used to gather such information by conversations with service personnel coming to Jaipur MES office for various purposes.
The Pakistanis used to ask him to send contact details of army officers posted in Jaipur and Bikaner, movement of army units, the state of Covid-19 in Jaipur cantonment etc. Mahesh Kumar revealed that he had given him bank account details to his Pakistani handlers, and he had received Rs 5000 on two occasions. However, it is suspected that he received more money and the same is being probed.
Although Mahesh Kumar’s main job is to clean offices, photos of several letters and notices, some with sensitive details, were found on his phone. Names of contact details of MES were also found in the phone.
Before his arrest, he had deleted all the chats with the Pakistani intelligence operatives. Although he had confessed to having sending information to Pakistan, it is suspected that he leaked more information that he had accepted.
In the month of February this year, eleven Navy personnel and two civilians were arrested for allegedly sharing sensitive information to Pakistani operatives through their social media profiles after being honey-trapped.