On April 25, a hacker group identified as ShinyHunters allegedly released data of 20 million Big Basket users for free on a hacker forum. The hacker wrote that the data file contains email, password (hashed), name, phone number, address, order details and other information of the users. It is believed that the data is from the infamous October 2020 breach. The information security firm Cyble Inc. had identified the breach and published a post on November 7 on its website.
What had happened in 2020?
As per a detailed report published by global threat intelligence SaaS provider Cyble, the alleged data breach happened on October 14, 2020. Cyble detected the breach on October 30 during its routine Dark Web Monitoring. The data was available for $40,000. Cyble validated the data, and on November 1, they informed BigBasket about the breach. The company urged them not to disclose the breach. Cyble advised them to let the customers know as they have the right to know about the breach.
On November 2, Cyble started informing the customers about the breach. VP-Engineering, Big Basket, approached Cyble for support and service, but Cyble refused, stating it was a high-risk engagement. However, later Cyble agreed to provide free/non-obligatory services. Big Basket was supposed to disclose the agreement between Cyble and Big Basket, but nothing happened from Big Basket’s end.
On November 7, Cyble made a public disclosure about the breach. On November 9, Big Basket acknowledged that the data was leaked. It has to be noted that not only the data of Big Basket but other companies were also compromised. Cyble later found out that the infamous hacker group ShinyHunters was behind the breach. On November 12, it was revealed that a threat actor identified as The Polaris had paid ShinyHunters $40,000 for the data.
Cyble named in FIR by Big Basket
Interestingly, Big Basket named Cyble in its FIR registered on November 6, 2020, with the cyber cell of the Bengaluru Police against the data breach. Cyble said, “Ironically, it appears that the complaint has made against Cyble itself – who was the informant of the breach aka “shooting the messenger. Cyble reportedly handed over the matter to its legal team to take appropriate action against Big Basket over alleged false accusations.
Disclosure by Big Basket
On November 10, Big Basket made a disclosure statement on social media platforms and said that as the company has been using OTP for login, there was no need to change the password. However, the company did not say anything about the other information like name, address, phone number etc., getting leaked.
Dear bigbasketeers,
— bigbasket (@bigbasket_com) November 10, 2020
Here is an update on the alleged cyber breach issue. We will keep you updated on developments. Thank you for your continuous support and trust.
Team bigbasket. pic.twitter.com/DvelBJq55B
“The only customer data that we maintain are email IDs, phone numbers, order details, and addresses, so these are the details that could potentially have been accessed. We have a robust information security framework that employs best-in-class resources and technologies to manage our information. We will continue to proactively engage with best-in-class information security experts to strengthen this further,” Bigbasket said.
After the recent uproar, the company again issued a statement and said that no further action required. However, it does not mention that the data leaked has personal information including name, address and phone numbers that can be used by scammers.
Dear bigbasketeers,
— bigbasket (@bigbasket_com) April 26, 2021
Here is an update on the alleged cyber breach issue.
Thank you for your continuous support and trust.
Team bigbasket. pic.twitter.com/BGY18Tmiuc
What is in the data?
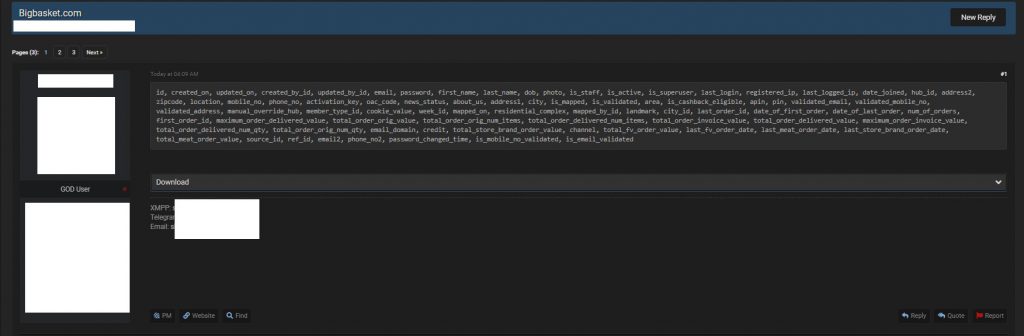
The SQL file that is available for free to download on the hackers’ forum allegedly contains full names, email IDs, password hashes (potentially hashed OTPs), pin, contact numbers (mobile + phone), full addresses, date of birth, location, and IP addresses of login among many others. OpIndia’s sources have revealed that the data made available by ShinyHunters on the hackers’ forum is legit, and it has all the information mentioned in the description. We cross-checked the information provided by our sources who had access to the data and confirmed it was true.
Experts’ views on the data breach
Alon Gal of UnderTheBreach said in a tweet thread, “To better understand how bad this type of hash is for the passwords, I can test 700,000,000,000 (700 billion) attempts at a password per minute with my RTX 3080.” “These passwords are essentially plaintext,” he added.
To better understand how bad this type of hash is for the passwords, I can test 700,000,000,000 (700 billion) attempts at a password per minute with my RTX 3080.
— Alon Gal (Under the Breach) (@UnderTheBreach) April 25, 2021
These passwords are essentially plaintext. pic.twitter.com/HI9dSMS5wm
While talking to OpIndia, Sourajeet Majumder, Independent Security Researcher, called it shocking and disappointing. He said, “The leaked dataset includes phone numbers and other details of many famous personalities as well who are possibly users of Big Basket. I even found my own PII data as a part of the dataset, which was quite shocking and disappointing for me.”
The leaked dataset includes user’s names, SHA-1 hashed passwords, address, emails, phone numbers, IP address besides other details (screenshot attached). Fortunately, it doesn’t include any Credit Card details. (2/3) pic.twitter.com/H6PjCSqnBy
— Sourajeet Majumder (@TechCrucio) April 25, 2021
He added that there are high chances that this dataset which has been publicly dumped, is the same dataset for sale a few months back. “Since the scale of this data breach is quite alarming, Big Basket must look into this asap and notify it’s users about this breach so that they can stay alert from any scam calls or phishing campaigns,” he added.
I believe this can be the same dataset which was being sold by “ShinyHunters” in 2020 for ₹30 lakhs. However, the scale of the breach looks quite alarming and @bigbasket_com should look into this asap !@troyhunt you may want to add this at @haveibeenpwned 🙂
— Sourajeet Majumder (@TechCrucio) April 25, 2021
(3/3)
To stay on the safer side, user’s too must change the passwords of their social media accounts, if they have been using the same password which they once used to sign up on Big Basket. Additionally, they can visit haveibeenpwned.com to check if their PII data was leaked in this breach.
Sunny Nehra, Admin at Hacks And Security, told OpIndia that Big Basket should come forward and inform its users about the corrective steps it has taken since the breach. He also insisted that users should change their passwords to be on the safer side. “As the data has a lot of personal information, I would advise Big Basket users to stay cautious of the malicious links in emails and messages. Scammers, hackers and threat actors can use such data breach to initiate scams that can lead to financial losses.”
Troy Hunt of HaveIBeenPwned said that the 52% of the breached data information was already available on the website. Additional information has been added, and users can check if their information was leaked.
Where to check if your information has been leaked?
Cable made the breached information available on AmiBreached.com. Android and iOS users can get full access to their services by downloading the mobile application. You can also check it on HaveIBeenPwned.com.
About ShinyHunters
The group has been active since 2015. Other aliases of the group are Shiny Hunters, #TheDarkOverlord, Gnostic Players. NightLionSecurity reported that in 2016 they started began terrorizing and extorting organizations. It gained popularity due to the extortion of medical providers and the sale of stolen medical records. In 2017, they started extorting companies like Disney, Netflix and others, saying they will release advanced copies of their productions if their ransom demands were not met. In January, they announced a “change of ownership” on Twitter. NightLionSecurity said that the actions taken as part of The Dark Overload can be traced back to a hacker identified as Christopher Meunier of Calgary from Canada.
Ways to avoid cyber attacks
- Do not click on any unverified or unidentified links in emails, messages or on social media platforms.
- Do not open attachments from untrusted senders.
- Download media from websites that you trust.
- Do not plugin unfamiliar USBs into your computer.
- Keep your security software updated and backup your data regularly.
- Keep your passwords unpredictable. Do not use names, birthdates and other identifiable information. Change passwords regularly.