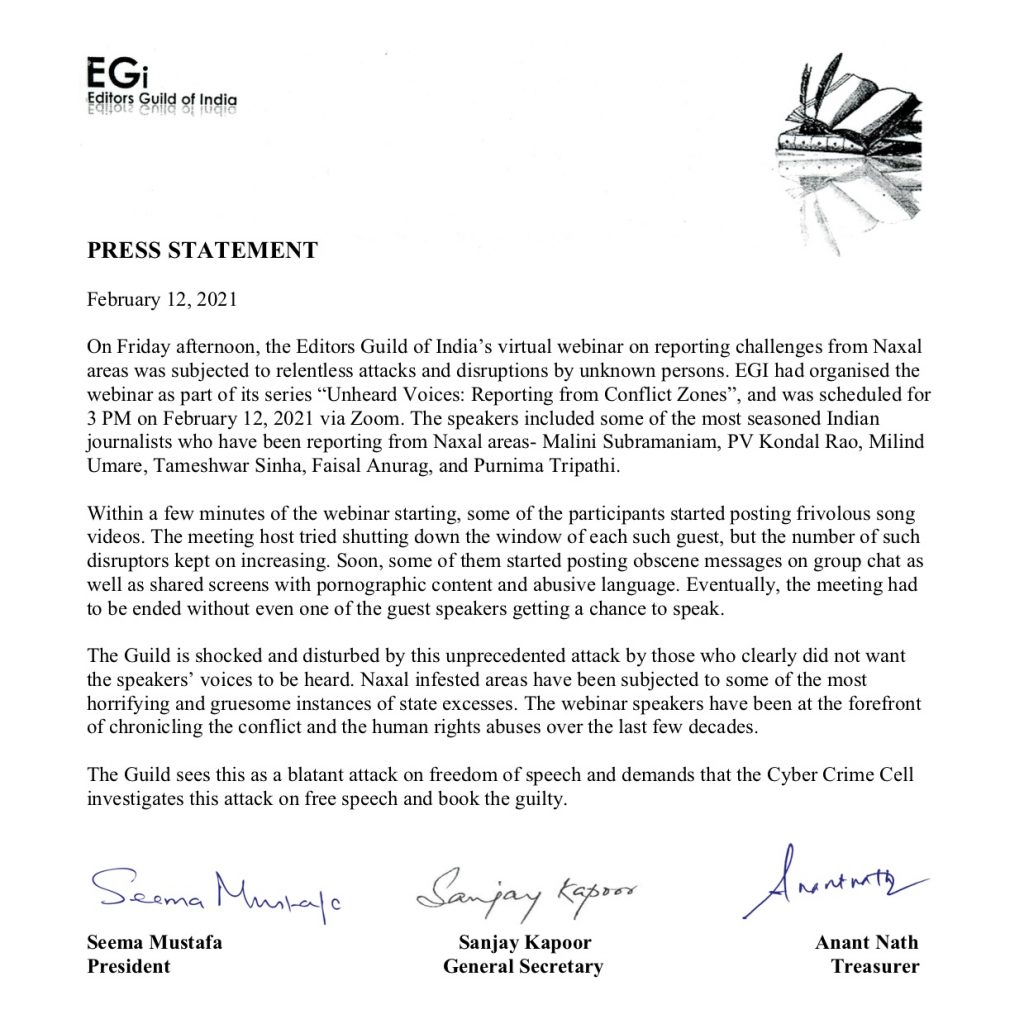
The Editors Guild of India took to Twitter today in order to condemn what they described as a ‘relentless disruption’ by ‘cyber attackers’. The EGI, which was hosting a webinar on Zoom, alleged that multiple ‘encroachers’ posted ‘obscene messages’ during the course of the webinar.
The webinar, titled “Reporting from Red Zones”, could only last for about 10 minutes due to incessant spam featuring ‘frivolous song videos’ followed by ‘pornographic content’, EGI alleged. The detailed statement from EGI called for an investigation on this ‘attack on free speech’ and called to ‘book the guilty’. However, if any video evidence exists to support the claim made by EGI, it hasn’t been released yet.
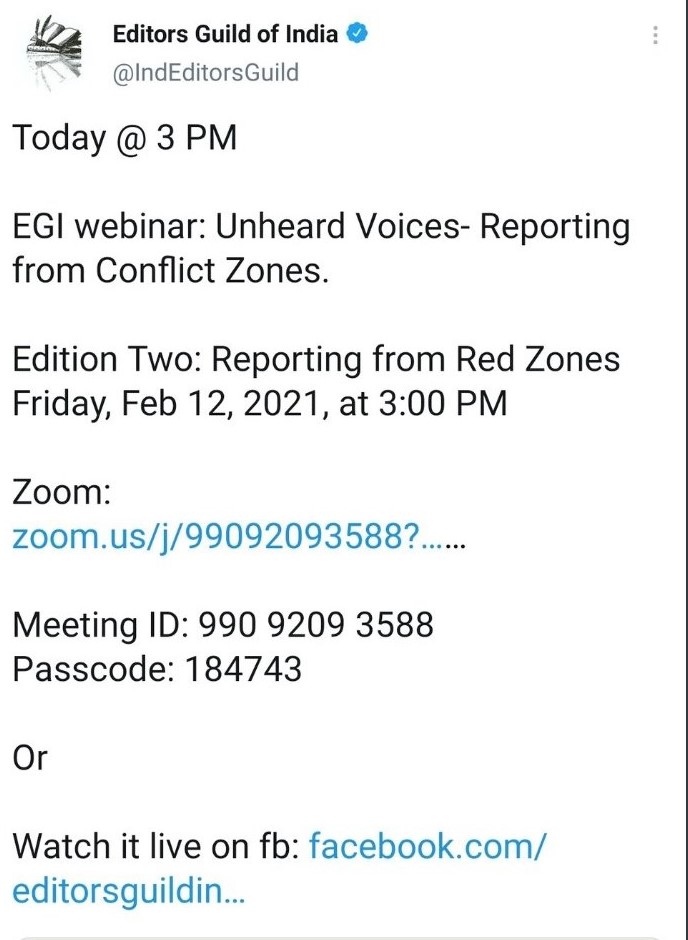
Before we dive any further into these allegations, we must keep in mind that this webinar was hosted on Zoom. Viewers had the ability to watch it through a Facebook live stream. One would think for a ‘cyber attack’ of this magnitude, “hackers” would need to utilize some sort of fancy malware to break into the Zoom meeting. But nothing of that sort happened. Actually, the EGI themselves tweeted out their Zoom meeting ID and passcode, which means there was no need for any ‘cyber-attacks’ or any kind of ‘hacking’ to access the online meeting. Any alleged miscreant who disrupted the webinar already had the passcode to enter available to him, thanks to the EGI itself.
It is certainly surprising that no video evidence exists online for this supposedly legitimate cyber attack. According to EGI’s statement, this cyber attack went on for at least 10 minutes, which would have given plenty of time to the numerous viewers of the webinar to record this extreme cyber-attack. But, unfortunately for EGI, they don’t really get a lot of viewers. The first edition of EGI’s webinar titled ‘Unheard Voices- Reporting from Conflict Zones’ had managed to attract a grand total of 24 concurrent live viewers, a paltry achievement for the EGI, which boasts of almost 34,500 followers on Twitter.
However, attracting 24 concurrent live viewers suddenly appears as a positive, when one considers the interactions that the EGI receives on both Facebook and Twitter. On Facebook, the EGI receives around 10 to 15 ‘reacts’ and 3 to 5 ‘comments’ on their posts on average. This is not discounting any negative ‘reaction’ or ‘comment’ that they might have received. On Twitter, they receive mid to decent interactions, specifically on tweets not related to the webinar. On tweets mentioning the webinar, the interactions resemble Facebook, with little to no interactions. At this point, it can be clearly stated that this is not a popular webinar by any means.
Thus, the question arises, why would ‘cybercriminals’ or ‘hateful trolls’ or whomever, target this supremely unpopular webinar that no one watches. It certainly wouldn’t be for attention or fame. It could be money, but is someone really paying ‘cyber criminals’ to conduct well-coordinated cyber attacks on a Zoom meeting with 24 viewers? Most probably not. So what could be the motive of these elusive ‘cybercriminals’, whose existence is not on video, to attack a zoom meeting with practically no viewers, it remains a mystery.
Here’s our theory, which is just a theory and not a factual claim. First of all, how did this tweet, which is about the webinar, manage to get a decent amount of interactions? Well that’s simple, liberal journalist Rajdeep Sardesai shared it with his followers. Without this plug, it is hard to say that anyone would have cared about the EGI’s statement, or that we would write an article about it. Most of the replies and people interacting with the EGI’s tweet are trolling or making fun of EGI. So to put it more clearly, the EGI needed Rajdeep Sardesai, with a whooping 9.1 million followers on Twitter to make a pity tweet so that anyone would even pay attention to them.
We have all heard the old adage, all publicity is good publicity. Maybe that is what was going on here. Maybe the EGI sabotaged its own webinar, to finally get anyone, literally anybody, to get them to pay attention and watch their webinar. However, if we are disregarding cynical theories and any maliciousness on the part of the EGI, another theory makes sense.
Maybe it is true, that there was some sort of raid, or coordinated trolling of the webinar. It sure was easy to do after the EGI itself tweeted the Meeting ID and the Passcode. In all probability, they were just random people instead of ‘hackers’ or ‘cybercriminals’, who the EGI is pushing to send to jail according to their statement. It is also a high possibility that the EGI greatly exaggerated the claims of the ‘cyber-attacks’ it had received, and the actual trolling was much milder. If we stop considering the possibility that this Zoom meeting raid was a work of malicious ‘cybercriminals’ instead of just regular, normal people, it becomes a much more believable story.