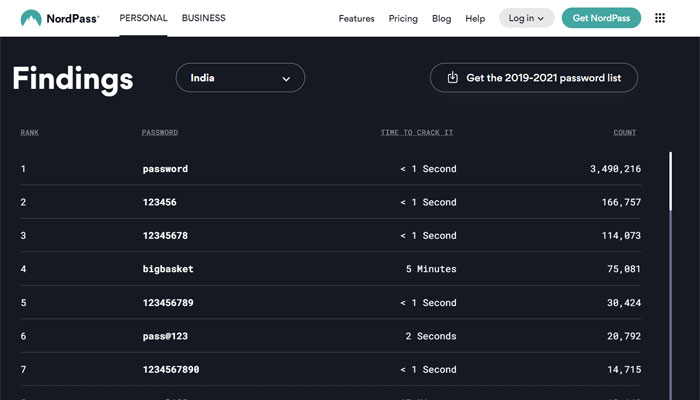
On November 15, Mint published a story based on NordPass’s report on passwords used by internet users around the world. In country-specific information, the report suggested that “password” was the most common password used, with over 3.4 million usages. “123456” was the second most used password. Surprisingly, “bigbasket” stood in the fourth position. Signifying the popularity of the online grocery store, the report claimed that it is the fourth most common password in India.
Big Basket assumed it was a PR worthy of info
Without going into the details of how NordPass generated the list, Big Basket flaunted the Mint’s report on its official Twitter handle, thinking this was something to be proud of. However, things were not in their favour as the information used in the report was based on data leak incidents.
Just found out that @bigbasket_com is using this for PR.
— Ravi Handa (@ravihanda) November 17, 2022
IDIOTS! pic.twitter.com/1N2dmWlD3r
In a now-deleted tweet, BigBasket wrote, “Keeping your partner’s name as the password (X). Keeping our name as the password (✔)”. However, as soon as they realised that it was nothing to be proud of and the list meant their servers were not robust and secure, the tweet was deleted.
Understanding NordPass’s report on common passwords
A Twitter user Ravi Handa published a detailed thread on the issue. Handa contacted NordPass to understand how they came up with the report on the most used passwords. In email communication, Handa asked NordPass about the source of the data.
I am sure by now you would have seen the list of “most common passwords of 2022”.
— Ravi Handa (@ravihanda) November 17, 2022
Probably you would have been surprised by seeing Bigbasket as no. 4 on the list. I sure was.
However, I would argue it is a matter of SHAME for BB and not pride. pic.twitter.com/OMeR8Vuvcc
In a reply, NordPass confirmed that they compiled the list in association with the independent researchers who evaluated 3-TB worth of data.
Why do I say so?
— Ravi Handa (@ravihanda) November 17, 2022
Because I did two things which almost none of the so called tech journalists did.
1 – Asked Nordpass (who made the list) for the source.
2 – Went through the list
Given below are screenshots of my email exchange. pic.twitter.com/Lnj8GlqJlQ
Interestingly, they clearly pointed out that the independent researchers they partnered with were experts in cybersecurity incidents. Furthermore, when asked where the 3-TB data came from, NordPass said they could not disclose the source as they had signed a non-disclosure agreement (NDA) with the source(s). NordPass also mentioned they had no access to the database of any company or server to collect the said information, which makes it clear that the password list came from the leaked data.
Furthermore, even the Mint report clearly suggested that the passwords were compiled based on the data analysed by data security experts. NordPass noted that 73% of the 200 most commonly used passwords this year were the same as last year. Around 83% of the passwords mentioned in the list by NordPass were easy to crack under a second, that include ‘password’ and ‘123456’. Hackers would take approximately five minutes to crack passwords in case of users using ‘bigbasket’ as their password, the report suggested.
The data security incident of 2020
Big Basket has been under the scanner for a data breach in October 2020. As per reports, data of around 20 million users was allegedly leaked then. In April 2021, a hacker group identified as ShinyHunters allegedly released the data for free on a hacker forum. The hacker wrote that the data file contains email, password (hashed), name, phone number, address, order details and other information of the users. It is believed that the data is from the infamous October 2020 breach. The information security firm Cyble Inc. had identified the breach and published a post on November 7 on its website.
As per a detailed report published by global threat intelligence SaaS provider Cyble, the alleged data breach happened on October 14, 2020. Cyble detected the breach on October 30 during its routine Dark Web Monitoring. The data was available for $40,000. Cyble validated the data, and on November 1, they informed BigBasket about the breach. The company urged them not to disclose the breach. Cyble advised them to let the customers know as they have the right to know about the breach.
On November 2, Cyble started informing the customers about the breach. VP-Engineering, Big Basket, approached Cyble for support and service, but Cyble refused, stating it was a high-risk engagement. However, later Cyble agreed to provide free/non-obligatory services. Big Basket was supposed to disclose the agreement between Cyble and Big Basket, but nothing happened from Big Basket’s end.
On November 7, Cyble made a public disclosure about the breach. On November 9, Big Basket acknowledged that the data was leaked. It must be noted that not only Big Basket’s data but other companies’ data were also compromised. Cyble later discovered that the infamous hacker group ShinyHunters was behind the breach. On November 12, it was revealed that a threat actor identified as The Polaris had paid ShinyHunters $40,000 for the data.
It is probable that the leaked data used to compile the common password list included data leaked from BigBasket, as there is a high probability that most people who used BigBasket as passwords are subscribers of the online store, and most probably they used it for their BigBasket accounts.
Disclosure by Big Basket
On November 10, Big Basket made a disclosure statement on social media platforms and said that as the company has been using OTP for login, there was no need to change the password. However, the company did not say anything about the other information like name, address, phone number etc., getting leaked.
Update:
OpIndia had contacted NordPass for details on the common password list, and they said that ‘bigbasket’ appeared as the 4th most common password in breaches that happened in late 2021 and 2022. This indicates that this data didn’t come from the breach of BigBasket user data that took place in 2020.
NordPass told OpIndia that the database used for the report is based on leaked data published on the Dark Web from data breaches that took place in 2022 around the world, along with some breaches in late 2021. The company said that they didn’t have access to raw data, they received already compiled lists of common passwords.