Early on Sunday, the United States launched a coordinated military strike on three of Iran’s most critical nuclear sites—Natanz, Fordow, and Arak. The strikes came amid rising tensions in the Gulf and growing concern over Iran’s nuclear breakout timeline. Precision munitions pounded infrastructure suspected of housing advanced uranium enrichment centrifuges and heavy water reactors. The immediate goal: cripple Iran’s nuclear development before it crosses a red line.
As per reports, US used its bunker busting bomb GBU-57 Massive Ordnance Penetrator (MOP) dropped from B-2 Spirit stealth bomber to strike the underground facilities. The 13,600 kg GBU-57 can penetrate deep into the grounds to destroy Iranian nuclear facilities located under mountains. The B-2 bomber flies at 50,000 feet altitude and is practically invisible in radar due to its stealth properties.
But while today’s headlines feature bombers and fighter jets, massive bombs, detailed military planning and coordination, this isn’t the first time Iran’s nuclear program has been set back by a foreign adversary. Over a decade ago, the most effective attack on Iranian nuclear establishment came not from bombs and missiles, but from a few thousand lines of code—discreet, invisible, and devastating.
No airstrikes, no bombs, just a sophisticated piece of malware that slipped silently into the heart of Iran’s enrichment facilities and blew centrifuges apart from the inside out.
This was Stuxnet—the world’s first true cyberweapon that caused physical damage to machinery. Not ordinary machinery, hi-tech equipment used in nuclear facilities.
The mission of the malware: delay Iran’s progress toward a nuclear weapon without triggering a full-blown war. Stuxnet silently damaged a lot of centrifuges at a Iranian nuclear facility even before anyone knew what was happening.
The Silent Sabotage
First discovered in 2010 but likely deployed as early as 2007, Stuxnet marked a watershed moment in cyberwarfare. It wasn’t just code—it was a precision-engineered digital weapon, designed to do physical damage to one of the most heavily guarded and secretive operations in the world: Iran’s nuclear enrichment plant at Natanz.
The worm was not designed to spy or steal, it sabotaged, manipulated critical machinery to self-destruct while feeding operators false data to mask the damage. It worked flawlessly for years before anyone even knew it existed.

Stuxnet was designed to spread from computer from computer running Microsoft Windows, and sit there, looking for presence of some very specific equipment connected to that computer. Specifically, it sought a specific Siemens software used to control industrial centrifuges, which are also used in nuclear facilities.
Stuxnet caused the Iran’s nuclear centrifuges to spin very fast and very slow, causing substantial damage. It is estimated that one-fifth of Iran’s nuclear centrifuges were destroyed by the malware. While causing the centrifuges to spin at unusual speeds, the malware also fed false data to the system, therefore the operators didn’t spot the malfunction.
Operation Olympic Games: The Architects of Stuxnet
The creation of Stuxnet was no amateur operation. Based on leaks, investigative journalism, and cybersecurity analysis, it’s widely attributed to a joint initiative between the United States’ National Security Agency (NSA) and Israel’s Unit 8200, under the codename Operation Olympic Games.
This partnership brought together unparalleled intelligence, industrial systems expertise, and cyber capabilities. The result was a worm that exploited four zero-day vulnerabilities—unprecedented at the time—and had the ability to mask its tracks, self-update, and even delete itself after completing its mission.
When the malware was finally discovered and experts looked into it, they knew that it was a work of govt agencies, not rogue elements. The creators went to a great extent to not damage any system not linked to Iran’s nuclear programs. Stuxnet just sat idle on computers if the specific conditions were not met. Moreover, it was designed to erase itself from infected systems on 24 June 2012.
The fact that four zero-day vulnerabilities were used in one program also confirmed that it was a govt program, as real hackers will use one vulnerability at a time, to maximise gains. Stuxnet represented a level of complexity, precision, and purpose never seen before in malware.
Of the four different zero-day vulnerabilities, one was so dangerous that it simply required having an icon visible on the screen – no interaction like clicking anything was necessary.
How Stuxnet Infiltrated and Attacked
Stuxnet had three components, a worm that conducted most of the work, a link file which automated execution of propagated worm copies, and a rootkit which hid files from detection.
Stuxnet was custom-built to target Siemens Step7 software used to program Programmable Logic Controllers (PLCs). These controllers governed the speed and operation of IR-1 centrifuges, the machines that spin uranium hexafluoride gas to concentrate U-235 isotopes—essential to creating weapons-grade uranium.
But Natanz was air-gapped—not connected to the internet. Therefore, it was not possible to infect the system remotely. Therefore, Stuxnet’s designers designed it to spread via infected USB drives, exploiting removable media to breach isolated networks. Once some unsuspecting engineer inserted an infected USB drive into his work computer at the nuclear site, the worm was inside the internal network, spreading to other computers on the network.
Once inside, it scanned the system for very specific configurations: the presence of Siemens PLCs running on Windows machines, connected to Vacon and Fararo Paya frequency converters, all operating within a particular range of speeds (807 Hz and 1210 Hz). This is a much higher frequency than motors typically operate at in most industrial applications.
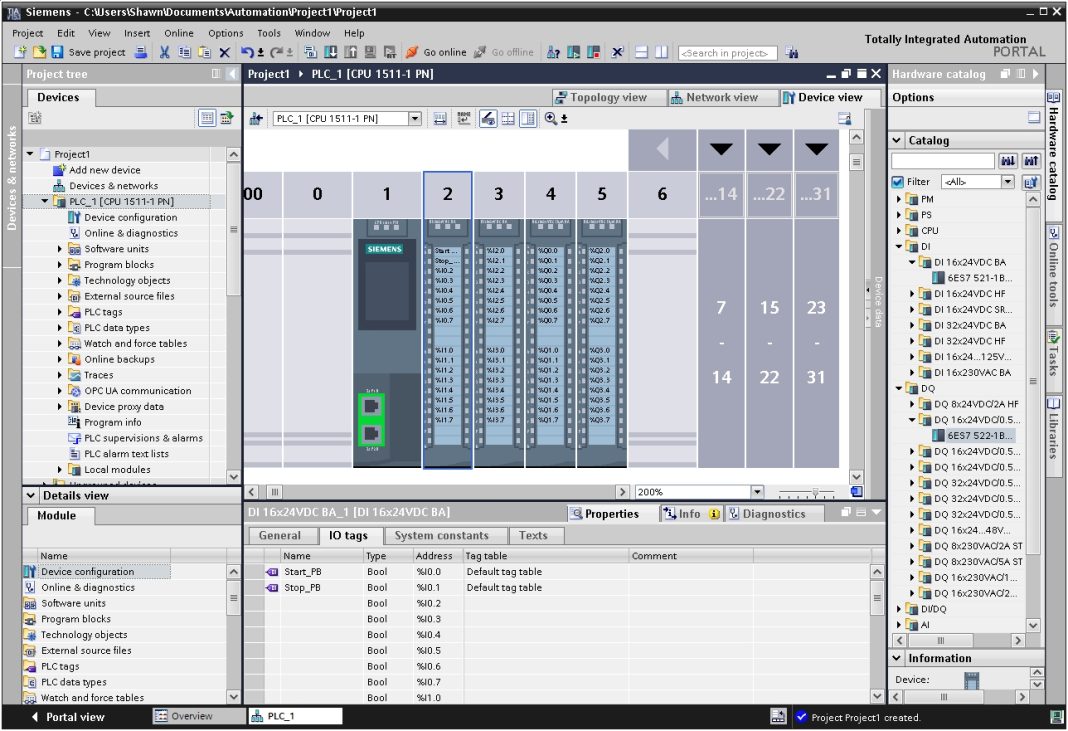
If those conditions were met, Stuxnet activated, and introduced the infected rootkit onto the PLC and Step7 software. It then modified the code to give unexpected commands to the PLC to spin the centrifuges at various speeds. It would subtly vary the centrifuge speeds in ways that stressed the rotors, causing them to crack and fail. It also reported normal status back to operators, hiding its activities.
The worm also included a rootkit, which hides the malware on the system and masks the changes in rotational speed from monitoring systems. The malware first increased the centrifuge speeds and then lowered it, and did it repeatedly. This caused excessive vibration, causing the centrifuges to tore themselves apart. Essentially, the malware caused the centrifuges to self destruct.

It was digital sleight of hand, and it worked. According to IAEA data and U.S. intelligence estimates, Stuxnet destroyed around 1,000 of the 5,000 centrifuges Iran had in operation at Natanz.
While initially spread via USB drives, Stuxnet was designed to be updated once it reached a computer connected to internet. Two websites in Denmark and Malaysia were configured as command and control servers for the malware for this purpose. It could also sent information on infected systems back to the control centres.
Global Fallout: The Worm That Escaped
For all its surgical precision, Stuxnet eventually escaped its target environment. In mid-2010, it was detected by a Belarusian cybersecurity firm, VirusBlokAda, on a client’s computer in Iran. The code had begun spreading outside Natanz, infecting industrial systems around the globe.
It appeared in over 100,000 systems across more than 155 countries. Most of these infections were benign—Stuxnet only triggered its payload under very specific conditions—but its global presence set off alarm bells. Researchers from Symantec, Kaspersky Lab, and others began dissecting the code, uncovering its unprecedented complexity and purpose.
The worm was designed not just to infect, but to hide in plain sight, avoid detection, and even remove itself when done. It used stolen digital certificates to appear legitimate, employed advanced rootkits, and had multiple fallback strategies for persistence. Its sophistication left little doubt: this was the work of a nation-state, not a hacker.
Though Stuxnet’s payload only executed under precise conditions, its spread revealed the vulnerability of global industrial systems. Factories, power plants, and infrastructure operators across the world were suddenly faced with the unsettling realization: a worm designed for one site in Iran had infected them too. While fast spinning centrifuges are not used in most industries, they are used in some specific sectors, like gas turbines.
While most systems were unaffected functionally, some Siemens-based control systems in India, Indonesia, and even the United States experienced abnormal behaviour or had to undergo security audits and partial shutdowns to ensure safety. Therefore, even thought there were no serious physical damage, firms had to spend considerable amounts of money and resources to fix the systems.
The incident forced governments and corporations to reevaluate cybersecurity for Operational Technology (OT)—the realm of hardware and software that controls industrial equipment. For the first time, IT security wasn’t just about data—it was about life.
The Beginning, Not the End
Once detected, Stuxnet was removed from the infected machines, and the vulnarabilities that it relied on were patched. Siemens released a detection and removal tool for Stuxnet.
Stuxnet was the first, but it wasn’t the last. It inspired a new class of malware— like Duqu, Flame, Triton, and Industroyer—each one more aggressive or more dangerous. Cyberweapons have since targeted Ukrainian power grids, Saudi petrochemical plants, and American pipelines.
Malicious software targeting critical infrastructure is no longer is a subject of Hollywood movies, it is happing in the real world. And it began with an attempt to shut down Iranian nuclear enrichment program.
As tensions escalate in the Middle East, and U.S.-Iran hostilities enter a dangerous new phase, the silent war continues beneath the surface: in servers, control rooms, high-speed internet networks and perhaps still in USB ports.